I’ve recently started the cryptopals crypto challenges, and, frankly, even the basics are kicking my ass. However, I seem to be enjoying them, and I’m finally starting to understand some of the Computer Science topics I really should have listened to at University. If you are like me and prefer learning by getting your hands dirty and hacking some code together, then I highly recommend working through some of these challenges.
Update 2023: Over the Christmas break, I finally managed to pick these challenges up again. The 4-year hiatus was due to me misreading challenge 7 and trying to implement AES myself. Something entirely unnecessary for the challenge and way beyond my abilities!
Cryptopals
If you have not heard about cryptopals before, then I'll leave it to the creators to explain:
We've built a collection of 48 exercises that demonstrate attacks on real-world crypto.
This is a different way to learn about crypto than taking a class or reading a book. We give you problems to solve. They're derived from weaknesses in real-world systems and modern cryptographic constructions. We give you enough info to learn about the underlying crypto concepts yourself. When you're finished, you'll not only have learned a good deal about how cryptosystems are built, but you'll also understand how they're attacked.
- The cryptopals crypto challenges.
I’ve been using these challenges to understand more about the internals of cryptography and the various attacks against them, but I’ve also seen these challenges used to learn new programming languages.
In this series of articles, I’m going to share some of my code and talk through the examples and theory that I found the most useful, hopefully along the way providing some eureka moments to others. These examples are not meant to be the most performant or best-designed code imaginable, but instead as a learning tool that clearly shows the functionality required to solve the challenge. Sometimes I go a bit off-piste and try to do something clever in C#. Unsurprisingly, this is often more trouble than it is worth.
DIY Crypto
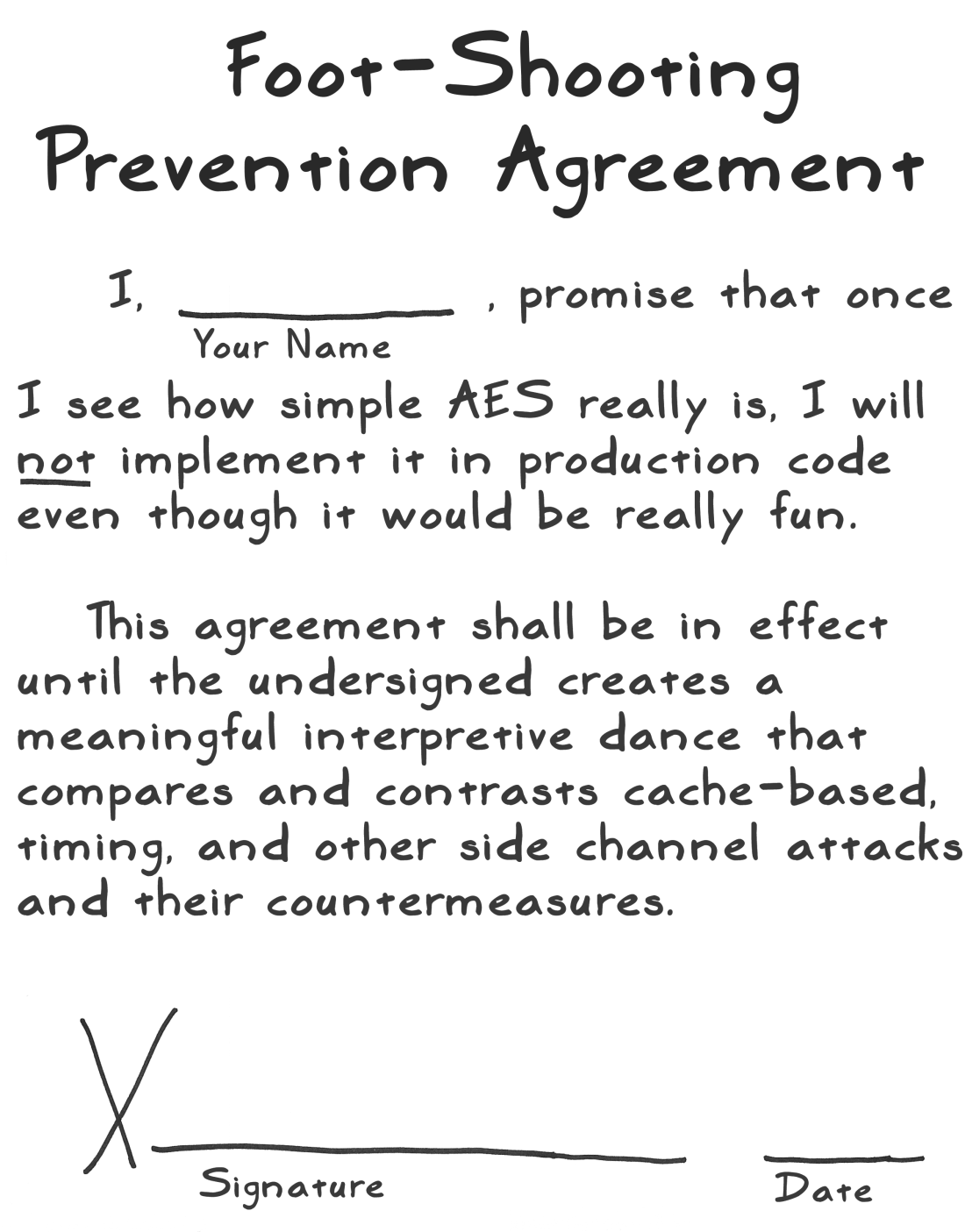
While it is a surprising amount of fun to implement cryptography, here’s a friendly reminder not to use any of this code in production. Stick to reviewed implementations.
Challenge write-ups
All examples were written and tested in C# and .NET unless otherwise stated.
Most people seem to quit at Challenge 6 or 8, so here’s hoping that I’ll stick with it! Spoiler: I did not, but it is taking me a very long time.
- Challenge 1: Base64 Encoding - implementing a custom Base64 encoder, dealing with hex strings, bit handling, and sextets
- Challenges 2-6: Caesar & Vigenère Ciphers - implementing and breaking XOR-based versions of the Caesar and Vigenère Ciphers
- Challenges 7-12: AES in ECB Mode - implementing AES with ECB and CBC block cipher modes and brute-force decrypting your first encryption oracle
- Spoilers for challenge 36: Secure Remote Password (SRP) in C# and .NET
Favorite Resources
- Serious Cryptography: A Practical Introduction to Modern Encryption by Jean-Philippe Aumasson
- Real-World Cryptography by David Wong
- A Stick Figure Guide to the Advanced Encryption Standard (AES) by Jeff Moser
